Hello laz,
I have a few questions.
- Would you please let me know the order of operations when a packet is being sent over a DMVPN protected with IPSEC tunnel?
My understanding is route lookup which is the tunnel interface-----GRE encapsulation-----IPSEC encapsulation—exit out of the interface. Please let me know if it is correct? - If the IPSEC tunnel goes down still I should be able to send out traffic through the GRE tunnel. The only problem is the traffic will not be encrypted. Is it correct?
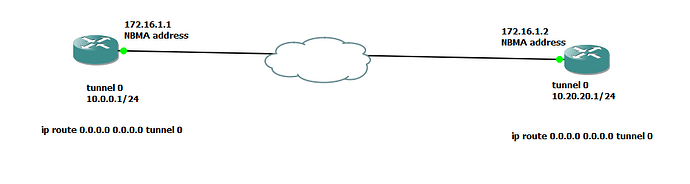
- For the sake of this conversation, let’s just say I have only one SPOKE in a DMVPN setup and I do not want to run any routing protocol over them. The tunnel IP addresses are from two different subents. If I configure static route pointed to the tunnel interface, should both hub and spoke not be able to communicate back and forth? Needs clarification.
Thanks as usual.
Azm