Hi
what is enhanced PAgP?
Hello Giovanni
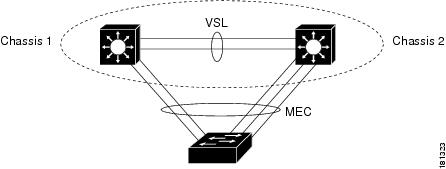
A dual-active scenario is when the standby chassis cannot determine the state of the active chassis, and it assumes that it is down, but it is not. If this happens, the standby chassis will go into active, and you’ll have two active devices in the VSS, which has adverse affects on network stability.
Enhanced PAgP is one of three methods that can be used to detect a dual-active scenario in VSS. In enhanced PAgP, PAgP messages are sent over the Multi Chassis Etherchannel (MEC) which is actually a connection to a third switch. This way if the VSL connection between the two VSS chassis is disrupted, they can still communicate with each other over a third switch. The following image shows the MEC and the VSL:
The following link describes how PAgP is used for dual-active detection: Catalyst 6500 Software Configuration Guide - VSS.
I hope this has been helpful!
Laz
Hello Walter
The VSS feature is strictly an IOS feature for the 6500, 6800, 4500, and 4800 series chassis type devices. The OS’es that you are showing here are Nexus series devices that run NX-OS. The Nexus devices are a different breed of equipment which are primarily used for datacenter and higher performance networks. NX-OS uses vPC configuration instead of using VSS. The concept is similar, but it is implemented on Nexus devices. Here is some info on how you can configure vPC on the NX-OS devices. The document is quite old, but the configuration and the principles are still valid:
I hope this has been helpful!
Laz
THANKS, LAZ!, is there a way you can show me how to effectively use the cisco documentation?, sometimes I get a little confused when I reach their website, how did come about accessing the config guide you gave? is there a method you use when navigating the cisco docs? how important are the Cisco docs in the real world?
Hi Walter
That’s a good question! Cisco’s documentation does need a little getting used to. Here are a few tips when searching Cisco documentation.
- First, I usually use Google to search rather than the Cisco site. This gives a broader range of search results, including both Cisco and non-Cisco sources. If I want a Cisco source, I make sure to put the word “Cisco” at the beginning of the search query. So “cisco vpc configuration” would be a good search query for the above document.
- When searching for a particular command, I usually put in the term “cisco command reference” before the command I am searching for. Cisco has CLI reference documentation for all of their commands, and this will typically provide me with the required entry within the document that I am looking for.
- Many of the questions that I’m dealing with have already been dealt with at least in part, in the Cisco community forums. Those too can be a good source of links to particular documentation.
- Even if you do find a document with the information you’re looking for, make sure to check its date. Much documentation may be over 10 years old and may refer to IOS versions that have been deprecated. Although Cisco is relatively good ad retiring older content, you can still find a lot of old documentation.
I hope this has been helpful!
Laz
I used your suggestion typing ‘‘cisco (topic) configuration’’, it really works. thanks for that great tip
Hi, vss creation and validation is great article. Thank you.
I am wondering what the chances are that you can take it a couple of steps further and include: VSS VLAN creation, new PO etc as the network evolves and expands.
Thanks,
/casey
Hello Casey
Thanks for the suggestion. You can go to the Member Ideas page to make any suggestions on content you would like. You can add this as well as any other suggestions you may have.
You may find that others have have suggested something similar, and if so, you can simply reinforce their suggestions by adding your voice.
I hope this has been helpful!
Laz
Hi,
I just wondered if there was anything available via free CML/Virl, Boson etc to allow practice of VSS config for the cat 6500/4500?
Thanks
Hello Frank
As far as I know, there is currently no way to lab up VSS on any emulator. In order to have hands-on experience, you must have access to such devices. However, all is not lost! On the one hand VSS is not that complicated so thoroughly reading up on it should be enough for any certification needs, and secondly, there are a lot of videos available where others have implemented VSS that you can follow along first hand.
I know, I know, there’s nothing like labbing something up to fully understand it. Unfortunately, because VSS is so hardware dependant, it’s not something that can be effectively emulated. It’s expected to be a very small part of the certification exam, so not to worry.
I hope this has been helpful!
Laz
Hi Laz,
Thanks for getting back to me.
I guess the important thing is to understand what is taking place, rather than trying to memorise commands.
Frank
hello Sir is there any particular licence required for VSS configuration on Cisco 4507E Switch , my both switches is rebooting continue and how can i stop this .
Thanks
Sukhveer Singh
Hello Sukhveer
Hmm, that’s strange behavior, but it is not unheard of. I found that someone else has had a similar experience with you with the devices rebooting:
Unfortunately, the thread above doesn’t give a solution to the problem.
The 4507E does support VSS but you may want to make sure that the IOS you’re using in both devices does support it. This documentation states that IOS XE 3.4.0SG and later support VSS. Also check that both devices are using the same supervisor engine version and that you have the same number of slots in both.
The only other thing I could suggest is because this is strange behavior it may be due to a bug, so reaching out to Cisco technical support is a good idea if you have a contract.
I hope this has been helpful!
Laz
Dear respective Team
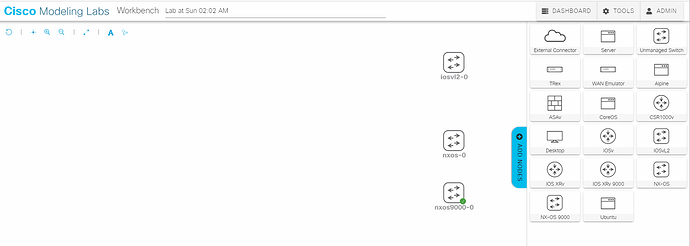
Im struggling of doing practice on this topic, would you support me how i can perform practice using Cisco Modling Lab (CML Virl2) ? i tried with IOSvL2, NX-OS and NX-OS 9000 in attachment
but couldnt find related commands! your support please
Hello Nahro
The VSS feature is only available on the 6XXX and 4XXX series catalyst switches, such as 6500 and 4500 for example. Because VSS is so hardware-specific, it has not been modeled in any network lab platforms that I know of, at least not in GNS3 or CML. And it doesn’t seem that any lab platform will model it any time soon, as it is a feature of a series of switches that are reaching their EOL.
The only way to practice with it is to use real equipment. Not to worry though, no need to go out and buy two 4500s (unless you really want to!), as this is a very small portion of any Cisco exam, if it appears at all.
I hope this has been helpful!
Laz
Sir Laz
Well noted, thanks for your time on replying my inquiry
Hello, everyone.
From what I’ve learned during my CCNP studies, the supervisor card contains the RP (the route processor) card along with some other components such as a console port, memory, etc.
Rene here mentions that he has a supervisor card that he uses to connect the devices together, so I have some questions.
- So supervisor cards can also have Ethernet/SFP ports on them? I found this from Cisco:
[image showing supervisor card with several Ethernet/SFP ports (removed for copyright reasons)]
Would we typically use the ports on a supervisor card to accomplish this? What about using a line card?
- Is VSS restricted when it comes to interfaces? Some resources say that it works with a 10-gig interface, even a 40-gig interface but it looks like not all of them are supported. Why? Also, does VSS do anything to pick the interface from which it will transmit VSS messages out of? Does it just automatically do this on interfaces that are supported, or?
- Is VSS typically only found on modular chassis devices? Like those big ones that are highly customizable. I’ve only seen VSS on them.
- When VSS is initiliazed, the RRP (Role Resolution Protocol) checks both device’s hardware and software versions to determine whether they are compatible. What happens if they are not?
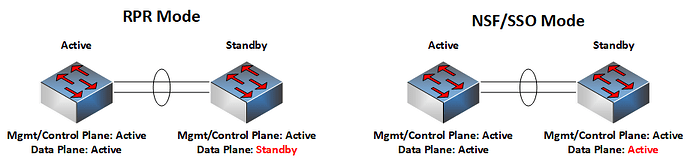
A Cisco document says that if they are compatible, the stack comes up in NSF/SSO mode (the standby SW along with the active are fully initiliazed and forward traffic). If there is, say a software or configuration mismatch, the stack comes up in RPR Mode which means that the standby switch is partially initiliazed and doesn’t forward traffic but acts as a backup if the active one fails.
In RPR mode, the active supervisor engine does not synchronize configuration changes or state information with the standby. The standby supervisor engine is only partially initialized and the switching modules on the standby supervisor are not powered up. If a switchover occurs, the standby supervisor engine completes its initialization and powers up the switching modules. Traffic is disrupted for approximately 2 minutes.
https://www.cisco.com/c/en/us/td/docs/switches/lan/catalyst6500/ios/15-4SY/config_guide/sup6T/15_3_sy_swcg_6T/virtual_switching_systems.pdf
This mode seems somewhat useless in terms of forwarding considering that the other switch is doing nothing, so I guess that’s another reason why our configuration should match.
If traffic arrives on the Active switch’s port and needs to be forwarded out of the standby switch’s port, shouldn’t this data traffic pass the VSL over to the standby switch? But the standby switch isn’t doing any forwarding, so what will happen here?
Thank you.
David
Hello David
Yes, supervisor cards do have ports on them. They can be used just like any other port on the switch (general data forwarding). However, they shouldn’t be used as regular network access ports. They are typically reserved for specific uses, including:
- out-of-band management
- monitoring (SNMP etc)
- high speed uplinks to core switches
- and of course using them as VSLs (Virtual Switch Links) to create VSS.
It is best practice to use these links as VSLs because they require low-latency, high-bandwidth links to synchronize control-plane and data-plane states between the two chassis. Supervisor ports are directly tied to the RP, ensuring optimal performance.
Yes. The prerequisites for an interface to act as a VSL are very specific. It is not only the speed of the interface. Indeed, a 10, 40, or 100G port is needed, but you must also have have hardware compatibility including the appropriate ASICs for control plane communication. A VSL when configured to function in this way, no longer acts as an Ethernet link, but as an extension of the control plane between the two switches. The signaling used is very different. Based on this Cisco documentation for example, only ports on the Sup720-10G supervisor or the WS-X6780 line card can be used as VSLs, because they have the appropriate ASIC capabilities for this. (for other platforms and newer devices, check appropriate documentation for compatible modules).
Yes, VSS is primarily designed for modular chassis switches like the 6500, 6800, or 4500-X.
This is because modular platforms support redundant supervisors and high-density/high-speed line cards which VSS leverages. Fixed switch devices like the 3850/9300 use StackWise technologies to achieve similar results, but these are distinct from chassis-based VSS.
It looks like the document is simply explaining the behavior of the system in the event of incompatibility. The RPR mode should not be used as a permanent deployment in a production network as the downtime in the event of a switchover is unacceptable.
Traffic will be dropped until the standby switch completes initialization and powers up its switching modules. Again, not an ideal situation, but that’s the behavior if there is incompatibility.
I hope this has been helpful!
Laz