This topic is to discuss the following lesson:
Hi Rene,
Nice Article . Please carry on .
br/
zaman
Hi Rene,
ASA1(config)# nat (OUTSIDE,OUTSIDE) source dynamic VPN_POOL interface
I got few doubt about the above statements
[1] Why is the key word SOURCE used in the NAT statement
[2] waht effect it would make if the Dynamic is changed to Static in NAT statment
STATIC is a one to 1 mapping ie public 8.8.8.8 maps to private 10.10.10.1 all the time.
DYNAMIC would be used if you had multiple connections that needed to be NATTed as you can then define a range of IP addresses using an access list and when a NAT translation needed to be made, then it would use a free public IP address from the access list.
Rene,
I was thinking through how to lab up this lesson and was having trouble on the layout for the cloud that labeled outside and the vpn user. I was thinking the cloud was a router with regular ospf passing all traffic and the vpn user… Could you point me in the right direction (configs) on how to lab up this lesson
thank you
Hello Christopher
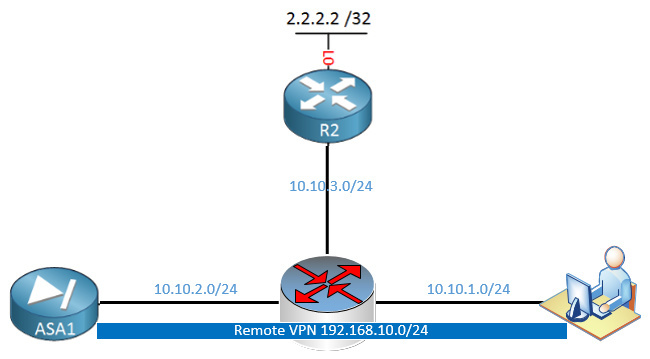
Yes, actually, you’re on the right track. You can create a router with three interfaces, each on a different subnet. Say something like this:
In this case, all of the 10.10.X.X address space can be considered “the Internet.”
You can use OSPF if you like to convey routing information to all routers involved, or you could use static routing if you like as well. Just keep in mind that both the ASA and R2 must be informed of each other’s networks (R2 should know about the 10.10.2.0/24 network and the ASA should know about the 10.10.3.0/24 and the 2.2.2.2/32 networks).
This way you can confirm that your VPN is working over “the Internet,” that incoming traffic to the ASA is entering via the VPN and outgoing traffic from the ASA will be connecting again via “the Internet” to the web server at 2.2.2.2.
I hope this has been helpful!
Laz
Hello Rene’
My question is that why would you even want to translate internal traffic or hairpinning for that matter, can you give any other examples.
thanks so much..
Irfan
Hi Irfan,
By doing this, we enforce that all remote user Internet traffic goes through our HQ ASA. Two reasons I can think of:
- We can filter Internet traffic from remote users on our ASA.
- Remote users might have a dynamic IP address. Imagine R2 is some remote development server which has an IP whitelist. Only the IP address of the ASA is on the whitelist. By using hairpinning, a remote developer can access the development server through the VPN.
Hope this helps!
Rene
Hello Rene,
Can you confirm a few details on this article please:
- The name split-horizon is used, should this be split-tunnelling?
- In each configuration example, Gi0/1 has been used for the interface detail, whereas the diagram uses Gi0/0. Is there some details I’m overlooking?
Thanks again for your help.
Hello Lee
Yes, you are correct, that should be split-tunnelling.
I see that on the ASA, Gi0/0 is the outside interface, while Gi0/1 is the inside interface. I don’t see G0/0 indicated anywhere in any configurations of the ASA, however, in all the configuration output it refers to this interface as OUTSIDE.
Having said that, I seen no configuration details of the actual Gi0/0 interface in the configuration files of the ASA.
I’ll let @ReneMolenaar know to make those improvements. Thanks for pointing this out!!
I hope this has been helpful, stay healthy and stay safe!
Laz
Hello Lee,
You are right, thanks for letting us know. I fixed “split horizon”, this should be split tunneling. I also fixed the interface number.
Rene
Hello,
command:
ASA1(config)# nat (OUTSIDE,OUTSIDE) source dynamic VPN_POOL interface
can be written:
ASA1(config)# object network VPN_POOL
ASA1(config-network-object)# subnet 192.168.10.0 255.255.255.0
ASA1(config-network-object)# nat (OUTSIDE,OUTSIDE) dynamic interface
Am I right?
Thanks!
Hello Marina
Yes, that is correct. This is the newer syntax that NAT uses when using what is known as object NAT. Detailed information about the command you used and the related syntax can be found here:
I hope this has been helpful!
Laz
I would like to know which software can I use to simulate the experiment.
GNS3, packet tracer or others?
Hello PO
Although I haven’t tried it, I am under the impression that you won’t be able to emulate this on PacketTracer. I would recommend GNS3 as it provides a more realistic environment to work with. Although, it would be a great exercise to attempt to create it on both. It would definitely not be a waste of time and it would be a learning experience.
In any case, let us know how you get along and if we can be of further help!
I hope this has been helpful!
Laz