That will allow you to telnet into the ASA yes.
Is it possible to port forward multiple services to the same server?
Hello Ryan.
Yes it is possible to port forward multiple services to the same server. You just have to make sure that you use different ports. For example, you can port forward the following services to the same internal server:
Inside global IP address/port number 55.29.29.29:80 to inside local address/port number 10.10.10.20:80 for web services
Inside global IP address/port number 55.29.29.29:22 to inside local IP address/port number 10.10.10.20:22 for SSH
Inside global IP address/port number 55.29.29.29:110 to inside local IP address/port number 10.10.10.20:110 for POP3
I hope this has been helpful!
Laz
Thanks for the example. I have been working on a similar case for ip cameras. This is port forwarding for two services to one inside host.
Part of the config works, part doesn’t.
Essentially, need port tcp 80 and port udp 37777 forwarded to the same inside host. The port 80 works, but only on the “inside”, not on the outside, and packet tracer says my port 37777 is failing.
object network CCTV-dvr
host 10.10.15.76
object service 37777_udp
service udp destination eq 37777
access-list outside-to-inside extended permit tcp any4 host 10.10.15.76 eq www
access-list outside-to-inside extended permit udp any4 host 10.10.15.76 eq 37777
nat (any,outside) source static CCTV-dvr interface service 37777_udp 37777_udp
object network CCTV-dvr
nat (any,outside) static interface service tcp www www
19 posts were merged into an existing topic: Cisco ASA NAT Port Forwarding
Rene,
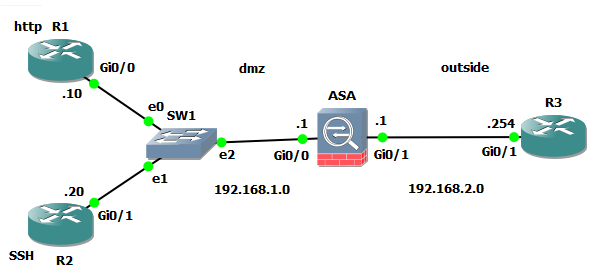
I have been following along this ASA lessons and am lerning a lot. I did have a question about the physical layout. On the DMZ side you have two fa0/0 port. how would the distant end look. Reason why I asked is that I would like to do a lab on this and wanted to test this out.
At first I was thinking two different ports with two slash 30’s but that would throw the lab off.
could you help me with this?
in the lab you type “R2#ssh -l cisco -p 10022 192.168.2.254” could you tell me what this is?
thank you in advance
Hi @chriscowboyfann,
From the ssh manual, the main description reads:
ssh (SSH client) is a program for logging into a remote machine and for executing commands on a remote machine. It is intended to provide secure encrypted communications between two untrusted hosts over an insecure network. X11 connections, arbitrary TCP ports and UNIX-domain sockets can also be forwarded over the secure channel.
ssh connects and logs into the specified hostname (with optional user name).
Spiritually ssh is the successor for telnet as a common way to access a CLI on a remote device. In this particular command syntax we are opening a connection to remote host 192.168.2.254 using port 10022 and attempting to login with the user “cisco”.
Best regards,
Jon
Hi,
I have a server on our DMZ (172.31.131.216), and I need outbound users to be able to connect to it via port 443. Here is my current config, does it make sense / do I need to adjust anything?
object network Melb_RT_Serv
host 172.31.131.216
nat (outside,dmz) dynamic* interface service 443 443
object-group Melb_RT_Serv
host 172.31.131.216
access-list Melb_RT_Serv permit tcp any object-group Melb_RT_Serv eq 443
*since our ISP has provided with a /27 network, would the dynamic command work here?
Hi Karl,
This config looks fine to me. With port forwarding, you’ll have to tell the router which IP address you want to use for translation, you can’t use dynamic here.
Rene
Hi Rene,
in your post you have the config:
ASA1(config)# object network SSH_SERVER
ASA1(config-network-object)# host 192.168.3.3
ASA1(config-network-object)# nat (DMZ,OUTSIDE) static interface service tcp 22 10022
Which means that if you connect to port 10022 on the outside interface, the request in forwarded to 192.168.3.3 port 80.
BUT what happens the other way around? What if the internal host 192.168.3.3 initiates the connection. It will be translated to the OUTSIDE IP, but will the port be changed as well? Is this translation only triggered if the specified ports are used?
Thanks for your help!
Hello Florian
These commands do the following:
Any communication from the outside with a destination IP address of 192.168.2.254 (the IP of the outside interface) and a port of 10022 will be translated and would reach the server at IP address 192.168.3.3 on port 22. These commands are ONLY for traffic originating OUTSIDE with the specific destination IP and port pair.
If 192.168.3.3 decides to initiate a communication to a destination on the Internet, these commands have nothing to do with the behaviour of such an action. If you want servers on the DMZ to access the internet, you must add an additional command/object. Details about this can be found at this lesson.
I hope this has been helpful!
Laz
Hi Laz,
thanks a lot for your reply.
What part in the syntax tells the router that this is only applicable for outside to inside communication?
The (DMZ,OUTSIDE) part, or what?
Regards
Florian
Hello Florian
According to Cisco, concerning the implementation of Network Object NAT:
When a packet enters the adaptive security appliance, both the source and destination IP addresses and ports are checked against the network object NAT rules. The source and destination address in the packet can be translated by separate rules if separate matches are made. These rules are not tied to each other; different combinations of rules can be used depending on the traffic.
Let’s take a look at your example:
ASA1(config)# object network SSH_SERVER
ASA1(config-network-object)# host 192.168.3.3
ASA1(config-network-object)# nat (DMZ,OUTSIDE) static interface service tcp 22 10022
For traffic originating outside and coming in, the following must be matched in order for this translation to take place:
- destination address of outside interface
- destination port of TCP 10022
For this same NAT rule to allow a translation to occur for traffic originating inside and going out, the following must be matched:
- source address of 192.168.3.3
- source port of 22
Translation will occur in this case, however, (as is the case with most services) port 22 is a listening port. It is designed to listen for incoming requests. The client server model is set up such that clients choose a random TCP port (somewhere between 49152–65535) and connect with the specific port of the service, 22 in this case being SSH. Although you can configure port 22 to initiate sessions, it is rarely done.
I hope this has been helpful!
Laz
Hi Laz,
thanks a lot for your help!
So here just the port number makes the difference?
And what is the “(DMZ,OUTSIDE)” for? Does this statement have anything to do with the direction the NAT rule works? Cant find anything about this.
Thanks
Florian
Hello florian
As mentioned in the Cisco quote, the command will function in both directions, however, the appropriate IP addresses and ports must be used in order for the transmission to match the NAT object and to successfully be translated.
As for the (DMZ,OUTSIDE) portion of the command, it must have the following syntax:
nat [(real_ifc,mapped_ifc)] …
The real_ifc is the real interface, that is the interface pointing towards the server/device for which you are configuring static NAT. The mapped_ifc is the mapped interface, that is, the interface to which you are implementing the NAT translation.
You can find more information about NAT on an ASA at this Cisco Documentation.
I hope this has been helpful!
Laz
Is there ever a scenario where you would need to configure NAT from outside to inside ie “nat (outside,inside)”? It seems like you could do pretty much everything you need with the “(inside,outside)” direction.
thank you.
Hello Bruce
Although it is true that the vast majority of NAT configurations are indeed nat (inside,outside), there are situations where the nat(outside,inside) scenario is useful. One such example is if you have a web server that is on the Internet that you want users on the inside of a network to access using an internal private address.
This example can be seen in the following Cisco documentation on pages 2 to 4 in a section titled “NAT for Inside Hosts (Dynamic NAT) and NAT for an Outside Web Server (Static NAT)”
I hope this has been helpful!
Laz
hello
in this topology i have few questions.
can I telnet from router R2 to R1 like
telnet 192.168.1.10 80 ? ( with port number)
if yes then i don’t know why i can’t.
I can telnet 192.168.1.10 ( just with IP but not with Port number)
I enabled IP HTTP SERVER on R1 already.
when I tried with port number it says it’s open but the connection never established.
I can telnet from R1 to R2 with and without port number and I can get access of R2 easily.
Thanks
Ankit
Hello Aniket
Yes, this is a valid command, you can add the port number you wish to use at the end of the command. However, in order for it to function, you require the Telnet server to be functioning and listening at the same port number that you are typing.
The command telnet 192.168.1.10 will use the default port number of 23. Because R1 is listening for Telnet sessions on this port, when you issue this command, it will work. By using the command telnet 192.168.1.10 80, you are instructing Telnet to attempt to create a Telnet session with R1 on port 80. But R1 is not running a Telnet server on port 80, but on port 23, so the attempt will fail.
The reason it said that the port is open is that port 80 is indeed open because you enabled the http server. Port 80 is used by the web or http server. So if you were to open a web browser and enter the IP address of R1, you would see the management web page of the device.
So when you connect to open ports, you must also use the appropriate application to access the desired feature. A web browser using HTTP should be used to connect to port 80 and a Telnet client to connect to Telnet.
It is possible to change the default ports used by particular applications if you choose to.
I hope this has been helpful!
Laz