Hi Filip,
Late reply from my end, just in case I checked this. On ASA 9.X:
ASA1# show version
Cisco Adaptive Security Appliance Software Version 9.8(2)
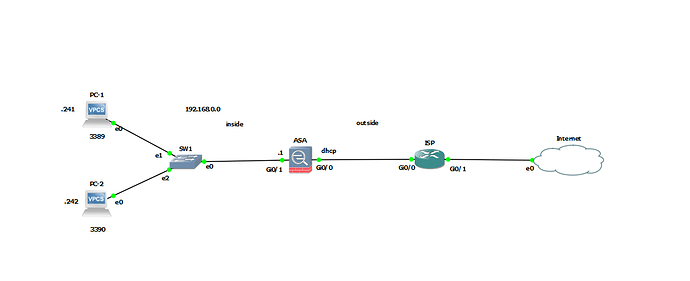
I have a simple setup with an INSIDE and OUTSIDE interface:
ASA INSIDE: 192.168.1.254
ASA OUTSIDE: 192.168.2.254
There is a host on 192.168.1.1 on the INSIDE, another host with 192.168.2.2 on the OUTSIDE.
This still works for me:
object network WEB_SERVER
host 192.168.1.1
nat (INSIDE,OUTSIDE) static interface service tcp 80 80
access-list WEB_SERVER extended permit tcp any host 192.168.1.1 eq 80
access-group WEB_SERVER in interface OUTSIDE
Quick test:
R2#telnet 192.168.2.254 80
Trying 192.168.2.254, 80 ... Open
What does packet-tracer tell you?
ASA1# packet-tracer input OUTSIDE tcp 192.168.2.2 12345 192.168.2.254 80
Phase: 1
Type: UN-NAT
Subtype: static
Result: ALLOW
Config:
object network WEB_SERVER
nat (INSIDE,OUTSIDE) static interface service tcp www www
Additional Information:
NAT divert to egress interface INSIDE
Untranslate 192.168.2.254/80 to 192.168.1.1/80
Phase: 2
Type: ACCESS-LIST
Subtype: log
Result: ALLOW
Config:
access-group WEB_SERVER in interface OUTSIDE
access-list WEB_SERVER extended permit tcp any host 192.168.1.1 eq www
Additional Information:
Phase: 3
Type: NAT
Subtype: per-session
Result: ALLOW
Config:
Additional Information:
Phase: 4
Type: IP-OPTIONS
Subtype:
Result: ALLOW
Config:
Additional Information:
Phase: 5
Type: QOS
Subtype:
Result: ALLOW
Config:
Additional Information:
Phase: 6
Type: NAT
Subtype: rpf-check
Result: ALLOW
Config:
object network WEB_SERVER
nat (INSIDE,OUTSIDE) static interface service tcp www www
Additional Information:
Phase: 7
Type: QOS
Subtype:
Result: ALLOW
Config:
Additional Information:
Phase: 8
Type: NAT
Subtype: per-session
Result: ALLOW
Config:
Additional Information:
Phase: 9
Type: IP-OPTIONS
Subtype:
Result: ALLOW
Config:
Additional Information:
Phase: 10
Type: FLOW-CREATION
Subtype:
Result: ALLOW
Config:
Additional Information:
New flow created with id 16, packet dispatched to next module
Result:
input-interface: OUTSIDE
input-status: up
input-line-status: up
output-interface: INSIDE
output-status: up
output-line-status: up
Action: allow
In your case, you could try:
ASA1(config)# packet-tracer input OUTSIDE tcp 1.2.3.4 12345 10.0.0.15 25565
About your other question:
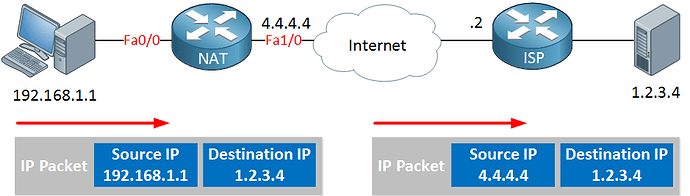
This is a good question, let me explain. The ASA supports Auto NAT and Manual NAT.
Auto NAT
- We configure this within a network object. That’s the only place where you can configure it.
- It can only make NAT decisions based on source traffic.
- It can only translate source traffic.
Manual NAT
- We configure this globally.
- It can make NAT decisions based on source and/or destination traffic.
- It can translate source and/or destination traffic.
My example is Auto NAT. Your example is Manual NAT.
With a simple port forward, Auto NAT is quick and simple. For more complex translations, you need to use Manual NAT.
With Auto NAT, NAT statements order themselves. With Manual NAT, you have to do this yourself.
If you use both Auto NAT and Manual NAT, you also have to consider the ASA’s preference:
1: Manual NAT
2: Auto NAT
It is possible to change the order so that Manual NAT statements are processed after Auto NAT.
In your case where you probably have one server behind your ASA, it really doesn’t matter much whether you use Auto or Manual NAT.
Hope this helps!
Rene