Hello Samuel.
Concerning your questions about sequence numbers:
I want to know if the last sequence number of the three way handshake is the same after the hanshake?
The quick answer is yes. Now for more detail. When a TCP session begins, a sequence number is chosen to begin the handshake. This very first sequence number is random. (However, if you look at the sequence numbers portrayed in Wireshark, you’ll see that it starts at 1. This is the RELATIVE sequence number, as it states in Wireshark. It is displayed in this way for simplicity.) Once the handshake is over and data is being sent, the sequence numbers that are used are in succession to the initial sequence numbers chosen during the handshake.
It only adds 1 when handshaking, but not during data transfer?
Yes, during the handshake, the ACK number that is returned by the second party is the original Sequence number plus 1. This is done to identify that this ACK is in response to the specific SYN request that started the handshake. So, during the handshake, the purpose of adding 1 is to indicate which request the acknowledgement is a response to.
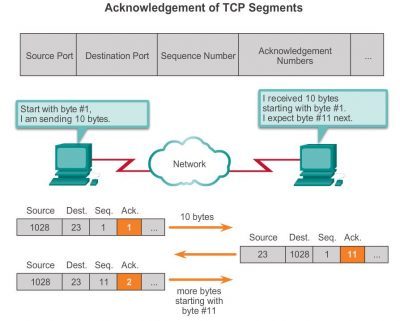
Once the handshake is complete, the sequence and acknowledgement numbers have a different purpose. They are no longer incremented sequentially, but they are incremented based on the number of bytes the host is expecting to receive before needing to send the next set of data. This functionality is part of a mechanism called Windowing or Window Scaling which Rene explains here: https://networklessons.com/cisco/ccna-routing-switching/tcp-window-size-scaling/
This mechanism with the sequence and acknowledgement numbers can be more clearly understood in the diagram I have attached to this post.
I hope this has been helpful for you!
Laz