Hello Guy,
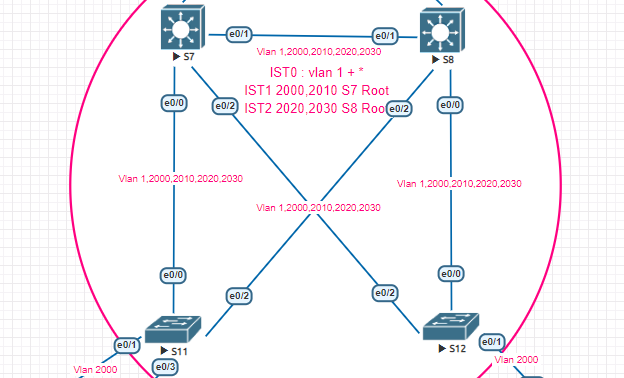
I’m currently doing some labs related to MSTP and there is something that I need to investigate :
On S8, I just do a simple “int vlan 2020; shutdown”, following this one, I can see many flap on other vlan interfaces so I was suspecting some events on my mstp topology and with the debug on S7 :
S7#
*May 23 10:25:39.435: %AMDP2_FE-6-EXCESSCOLL: Ethernet0/3 TDR=0, TRC=0
S7#
*May 23 10:25:43.373: %VRRP-6-STATECHANGE: Vl2020 Grp 202 state Master -> Backup
S7#
*May 23 10:25:43.690: MST[0]: Et0/1 disputed
*May 23 10:25:43.690: MST[0]: Et0/1 state change forwarding -> blocking
*May 23 10:25:43.690: MST[1]: Et0/1 state change forwarding -> blocking
*May 23 10:25:43.690: MST[1]: Et0/1 disputed
*May 23 10:25:43.690: MST[0]: sending proposal on Et0/1
*May 23 10:25:43.690: MST[1]: sending proposal on Et0/1
I understand thanks to your course why I see the dispute message in my debug (after my action, BPDU received from S8 we can see port role changed from root to Designated) but I still don’t understand why this simple action on vlan interface number 2020 caused this mess.
Vlan 2020 belongs to MSTI 2. We can see the first notification is the vrrp role changement which is as expected.
Any clue on this one ?
Yoann