Hello Donald
There is no way to prevent VTP from sending information about specific VLANs to other switches. In other words, there’s no way to directly filter which VLANs are shared and which are not. VTP will automatically take the VLANs on the VTP server and share them with all VTP clients in the same domain. The only way to achieve it is to use the transparent switch you suggest in your post.
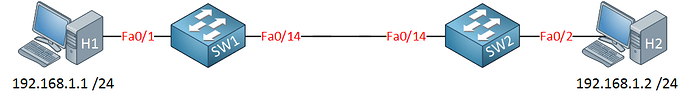
However, remember that if you have VTP pruning enabled, it will “prune” VLANs on the trunks that connect to switches that are not using those particular VLANs. What does that mean? Well, take a look at this topology:
Now imagine that the link between the switches is a trunk, and both VLANs 1 and 50 are allowed on that trunk. Now imagine that H1 and H2 are connected to access ports on VLAN 50, and SW1 has no access ports on VLAN1. Therefore, even if SW2 has some host on VLAN 1, no traffic belonging to VLAN 1 should ever traverse the trunk. If it does, it will simply be dropped, since there are no hosts on VLAN 1 on SW1.
That means that VTP should prune VLAN 1 on the trunk. What does that look like?
SW2#show interface fa0/14 trunk
Port Mode Encapsulation Status Native vlan
Fa0/14 on 802.1q trunking 1
Port Vlans allowed on trunk
Fa0/14 1-4094
Port Vlans allowed and active in management domain
Fa0/14 1,50
Port Vlans in spanning tree forwarding state and not pruned
Fa0/14 50
You can see that VLANs 1 and 50 are allowed, but only VLAN 50 is not pruned. Therefore VLAN 1 is pruned.
So what is my point? Well, even if VTP shares all existing VLANs with all other switches, those VLANs exist as entities in the VLAN database, BUT, VTP pruning will eliminate any unnecessary VLANs from transmitting over a trunk.
For more info about the above configuration take a look at this lesson:
For more info about VTP and pruning take a look at this Cisco documentation:
I hope this has been helpful!
Laz