Hi Rene and staff,
i was doing a basic lab ipv6 with GNS3 and SSH came in front of the scene (no matter ipv4 or ipv6 in this post)
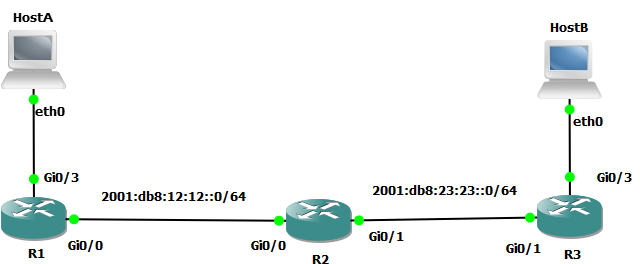
This is the lab
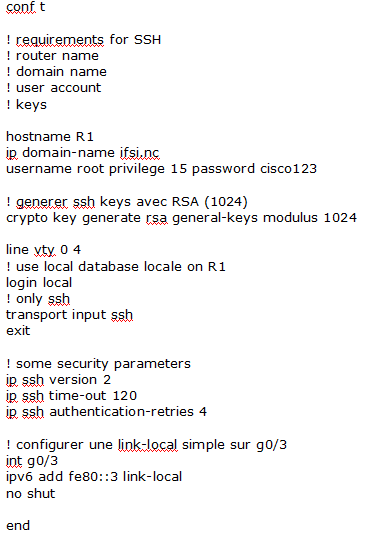
and opening SSH session from HostA to R1 led me to review crypto keys with cisco (just to remind)
R1 configuration is
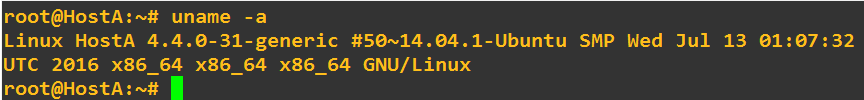
Host A is toolbox
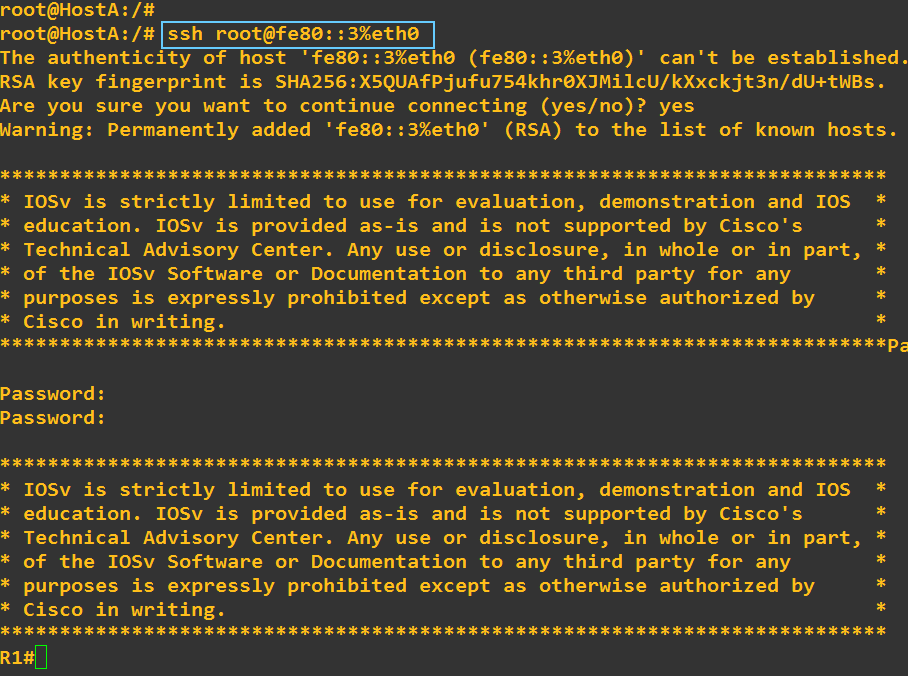
I opened the ssh session
Sorry, i failed the password twice
And exit the session
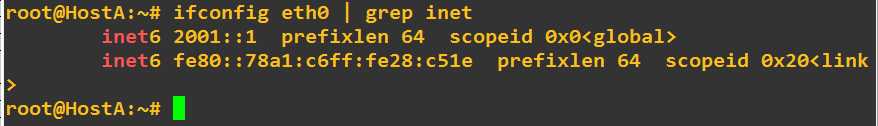
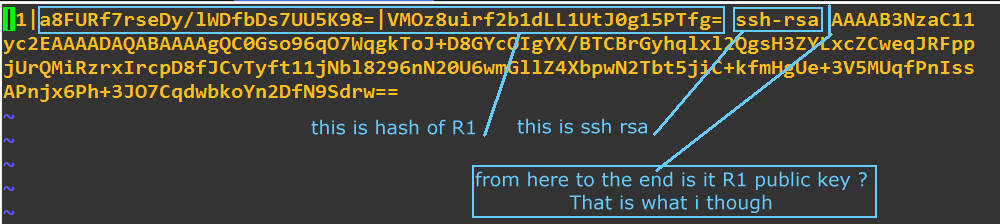
At this step, my question is about to find the public key of R1 in hostA
Going to hostA here is what i found
(vi /root/.ssh/known_hosts)
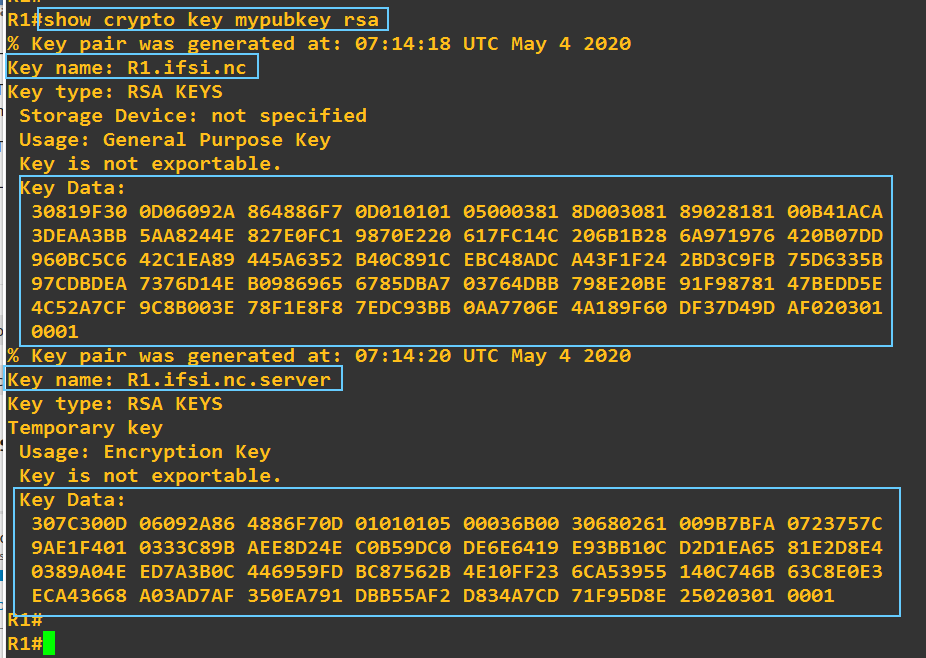
Going to R1 here is what i found
Key data on R1 seems not to match with the content of the file known_hosts in the client hostA: that is what i want to understand
If i am in a wrong way please tell me so i could understand
Regards