Hello, everyone.
What exactly is the difference between normal/class policy maps and those that use type inspect?
I understand that the second option is used with the ZBFW configuration on cisco IOS routers. What exactly does the type inspect indicate, though?
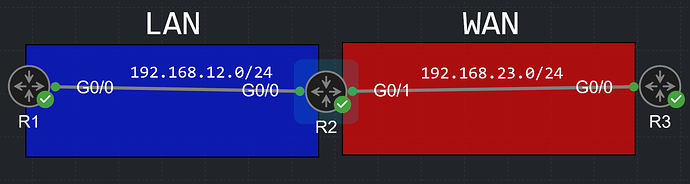
Also, I have the same topology as Rene:
R2(config)#zone security LAN
R2(config)#zone security WAN
R2(config-if)#int G0/0
R2(config-if)#zone-member security LAN
R2(config-if)#int G0/1
R2(config-if)#zone-member security WAN
R2(config)#ip access-list extended ANY
R2(config-ext-nacl)#permit ip any any
R2(config)#class-map type inspect ANY
R2(config-cmap)#match access-group name ANY
R2(config)#policy-map type inspect ANY
R2(config-pmap)#class ANY
R2(config-pmap-c)#inspect
R2(config)#zone-pair security LAN-TO-WAN source LAN destination WAN
R2(config-sec-zone-pair)#service-policy type inspect ANY
I can ping from R1 to R3
R1(config-if)#do ping 192.168.23.3 repeat 1000
Type escape sequence to abort.
Sending 1000, 100-byte ICMP Echos to 192.168.23.3, timeout is 2 seconds:
!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!
!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!
And while that ping is active, I can ping from R3 to R1
R3#ping 192.168.12.1 repeat 10
Type escape sequence to abort.
Sending 10, 100-byte ICMP Echos to 192.168.12.1, timeout is 2 seconds:
...!!!!!!!
Any idea why? I understand that the router will inspect the ICMP request, allow it to pass, and create some rules for the replies, however, this allows R3 to also initiate ICMP requests to R1 until some timeout for that flow expires I suppose.
If I try it a minute later, it doesn’t work of course, it only works when R1 is pinging R3 or a few seconds after the ping ends.
R3#ping 192.168.12.1 repeat 10
Type escape sequence to abort.
Sending 10, 100-byte ICMP Echos to 192.168.12.1, timeout is 2 seconds:
....
It doesn’t of course work with protocols like Telnet
R1#telnet 192.168.23.3
Trying 192.168.23.3 ... Open
**************************************************************************
* IOSv is strictly limited to use for evaluation, demonstration and IOS *
* education. IOSv is provided as-is and is not supported by Cisco's *
* Technical Advisory Center. Any use or disclosure, in whole or in part, *
* of the IOSv Software or Documentation to any third party for any *
* purposes is expressly prohibited except as otherwise authorized by *
* Cisco in writing. *
**************************************************************************
User Access Verification
Password:
R3#telnet 192.168.12.1
Trying 192.168.12.1 ...
What could be causing this for ICMP? Does the reply rule only work on an IP-address basis? Does R1 not know that R3 is actually initiating the ping and not responding to the ping initiated by R1? 
Next, what exactly does this value indicate? (The 2:0). When a packet is inspected via a firewall (or a cisco router  ), the control plane is also involved, or not? So this basically says that 2 packets were process-switched.
), the control plane is also involved, or not? So this basically says that 2 packets were process-switched.
policy exists on zp LAN-TO-WAN
Zone-pair: LAN-TO-WAN
Service-policy inspect : ONE
Class-map: ONE (match-any)
Match: protocol telnet
1 packets, 24 bytes
30 second rate 0 bps
Match: protocol icmp
1 packets, 80 bytes
30 second rate 0 bps
Inspect
Packet inspection statistics [process switch:fast switch]
tcp packets: [2:0]
And one more thing. Say that I configured my zones in a way where LAN can initiate connections to the WAN but WAN cannot initiate connections to the LAN. If LAN is configured under the inspect option, this means that WAN will be able to talk to the LAN as long as WAN is responding to LAN and not trying to initiate any connections to it, correct?
Then, if we configure a zone such as LAN and assign it to an interface via the zone-member command, will this interface be part of the LAN zone or the self zone?
And one last thing. Say that the LAN zone has 20 hosts, each of them should only be able to use ICMP to reach the WAN however, one host can use any protocol to reach the WAN. How would we configure this?
Thank you.
David