Where can I get a resource for designing a network for Internet-based business?
Thanks
Hello Abubaker
Unfortunately there’s no silver bullet that will be able to resolve any and all requirements of a business regardless of its particular focus. In order to come up with a design, detailed network design specifications must be determined. This is done by determining the size of the business, what kinds of applications they will be running, what bandwidth per user and per network will be required, the number of physical locations they will have, and the number of remote employees as well. You must also determine if this network will serve only the employees, only the customers, or both. The design must also include things like security and redundancy, especially since we are talking about an internet-based business.
This lesson provides you with an overview of the process you should follow in order to determine the requirements, and translate those into a design.
I hope this has been helpful!
Laz
while reading Campus Wired LAN Technology Design Guide the paragraph below mentioned a seperate management vlan should not be configured for directly connect router or firewall. Can you explain why?
If the switch is the only switch at the site and is directly connected to a router or
firewall, do not configure a management VLAN. Instead, use the data VLAN for both
data and switch management. When you use this configuration, the next step requires
that you also configure the in-band management interface VLAN using the data VLAN
ID. For example:
interface vlan [data vlan]
description In-band switch management using data VLAN
ip address [ip address] [mask]
no shutdown
Hello Donald
I’m assuming that this single switch is an L2 switch. If this is the case, then this is good advice.
Imagine you configure a management VLAN on the switch. Imagine also that the administrator’s PC is connected to a port on the data VLAN of the switch. In order to reach the SVI of the management VLAN, the communication must be routed. This means that any such communication on the data VLAN would first go to the router or firewall, be routed, and come back on the management VLAN to reach the management SVI. This is fine, however, in the event of a failure of the router or of the link to the router, all communication with the management SVI of the switch will be lost.
I hope this has been helpful!
Laz
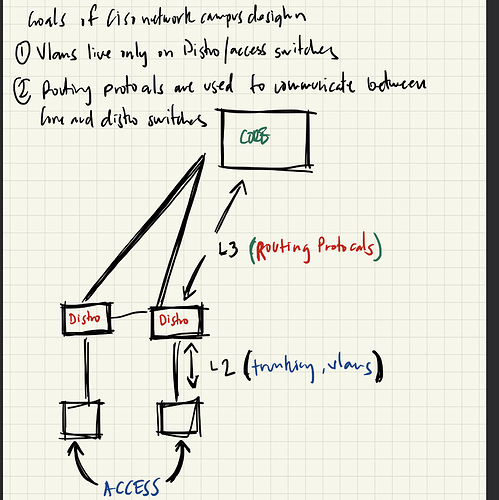
Just for clarification I’d like to ask, is the goal of Cisco campus networking to do the pictured?
- Vlans are to live on distro and access switches?
- Routing L3 protocols are to be used between distro and core switches.
Hello Derrick
When designing a network, the intention is to limit the physical scope of VLANs to particular Access and Distribution switches, in order to avoid spanning L2 traffic across large distances.
Similarly, routing is kept, as much as possible in the Distribution and Core layers as you suggest.
Similarly, features such as PoE, STP, Port Security, QoS are limited to the access layer, while routing, and security access lists are applied in the distribution layer
This is what we try to achieve using the hierarchical model, but as with all rules, there are exceptions. You may need to span a VLAN across multiple distribution modules or employ routing lower in the model, but these should be very limited and only if absolutely necessary for your requirements.
I hope this has been helpful!
Laz
So… I’m correct in what I’m thinking?
Generally speaking yes, but I would say the goal of network design is to identify the requirements and implement a design that meets those requirements. Adding unecessary layers, protocols etc will just complicate things.
Taking your design as an example, you wouldn’t need routing protocols as there is only one path to the core which is a single point of failure (assuming you don’t have hundreds of routes). You also wouldn’t need three distinct layers with such a small network.
Some networks will warrant a distinct three layer approach with L2 only at the access layer, a collapsed core with L2/L3 in the dist/core layer will be sufficient in others.
It depends! ![]()
Hello Derrick
I agree with @stevedblue that it depends. As a general starting point, however, for the three tier model, yes, you are correct in your thinking. That’s where you must start from, and based on the specific requirements, build on that.
I hope this has been helpful!
Laz
Hi,
When we connect access switches to distribution switches, is it a requirement have the uplink faster than other access ports??.
For example.. If I have 1 24port gigabit unmanaged switch as access level..can I connect directly with one of these ports to the distribution layer? Does this design cause bottleneck or congestion issues?
Thank you
Hello Giovanni
In general terms it is always a good idea to have your uplink be faster than the ports of the access switch that are serving end devices. If you have a 48 port GigabitEthernet switch, and you have a single GigabitEthernet uplink, you can imagine the kind of bottleneck that can potentially occur.
A lot of this will also depend on the applications being run by the user devices. If users only use email and web surfing without any video (such as YouTube or Vimeo), then it may actually be OK to do that. But you can never be sure how traffic patterns may change over time. In general, your uplink should be multiple times faster than the end user devices that connect to your access switch.
I hope this has been helpful!
Laz
Thanks,
In the case that better hardware is not available…does a port-channel provide a solution for this design?
For example provide 2 links to give more bandwidth for uplinks ( I know that is not the same thing) but can it be considered a solution for possible bottlenecks?
Hello Giovanni
Yes, a port channel would be a solution to such a problem, but not an ideal one. Etherchannel will only increase the uplink speed by the number of physical links that are available. Much higher throughput will be achieved by using faster interfaces, because the increase in speed is usually 10 times. For example, Gigabit Ethernet is 10 times faster than FastEthernet, and 10G interfaces are 10 times faster than GigabitEthernet… and so on.
But definitely, in the absence of any other solution, etherchannel is a good solution.
I hope this has been helpful!
Laz
Hi There,
Thank you for taking to time to visit this thread.
Would you guys share, any books or training resource that can teach for small & medium and also medium & large enterprise design.
Preferably vendor neutral.
Hello Saravanan
Enterprise network design is an extremely interesting and challenging topic. To get you started, I can share a few links and thoughts with you, but they will be more Cisco oriented. Cisco has developed an enterprise network design philosophy called Digital Network Architecture (DNA). They define it as an “open, software-driven approach to software-defined and intent-based networking”. It goes beyond the hierarchical two- or three-tier model, and introduces SDN and network orchestration. You can find out more about it in detail at the following online location that includes A LOT of resources:
I’m not sure what level of expertise you are looking for, but to avoid information overload, you can begin by looking at the following lessons which are a more basic beginning to working up towards DNA:
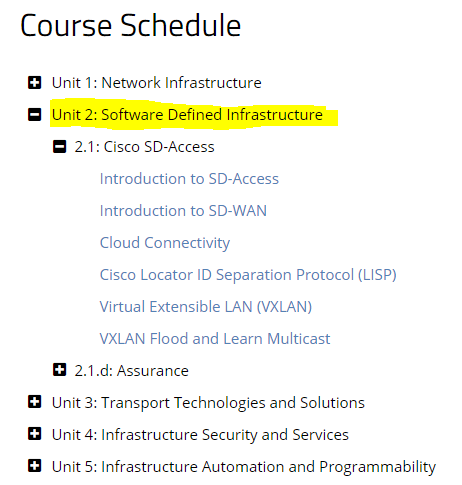
You can also take a look at Unit 2 of the CCIE Enterprise Infrastructure course here on NetworkLessons that deals with software-defined infrastructure.
Now as for vendor-neutral information, doing a bit of research, I found that even self-proclaimed vendor-neutral sources often refer back to Cisco documentation and practices simply because it is so well put together. Remember that a lot of the Cisco documentation and certifications can be applied in principle to other networks. One good starting point is the certification content for the CCDE certification exam which is an expert level network design course.
I hope this has been helpful!
Laz
Hi Laz,
Seems that you’re the network guy alive during this time. ;).
Thanks for reply, I agree it’s easier to follow Cisco certification and documentation.
![]()
HI,
In these days we have to design a new network for a campus university.
I have any question about what the best practice says about that:
-
Should we have to bring all workstations cables into a rack room and put the access layer - distribution layer in the same room, or should I put a rack into each classroom and bring only the cables of the uplink??
-
In the case I have few computers to connect (1 or 2 ), Is the worth to put another layer of switching for the access layer ,or maybe in this case, I can connect directly to the distribution layer? (like a spaghetti example of Rene)
-
Should I design a spine and Leaf architecture for a campus university?
-
How can design a network redundancy for the workstations on each classroom?
Thank you so much
Hello Giovanni
These are excellent questions, and I’ll try to address each one as well as possible.
Ideally, the access and distribution layers should not be in the same location. The access layer’s role is to be as close as possible to the end devices so that cable lengths can be limited to under 90m (which allows for 5m patch cords on each end) or much less if possible. The distribution layer should not be that close, but should be able to consolidate multiple access layer switches in various locations. If you have enough endpoints in a single classroom, then putting a rack in each room is not a bad idea (as long as you have redundant power, and you can successfully restrict access to the equipment). You can then use fibre to link multiple classrooms to a single distribution switch location without the limitation of cable distances.
Ideally, you should have an access layer. However, when money is involved it is often an incentive to compromise. in this case, it’s probably not worth the cost of an access switch with redundant power, and a rack and so on (which in some cases can be in excess of €1000), just for two computers. Connecting directly to the distribution switch is probably better, but is still an exception to the rule. Just make sure to document this clearly in both paper documentation as well as in the description of the ports in the devices.
The spine and leaf architecture is typically used more for datacenters rather than enterprise networks. If you are designing the datacenter as well, then you can examine this as an option, but for the campus network, you should stick to a more traditional 3 tier network.
Network redundancy is not typically designed into the access layer of a network. In order to achieve network redundancy for each workstation, you literally need to have two network cards on each computer, and connect each one to a port on a different network switch. This drastically increases the cost of structural cabling and the number of access switches you (double the number of ports and cables.).
However, redundancy can be achieved on the switches themselves by employing redundant power supplies and stackwise implementations that support sending power over the stackwise cable. This way even if a component of the access switch fails, the switch itself will not fail. This is a more financially viable solution, to beef up the access port switches, rather than provide redundancy all the way to the workstation.
I hope this has been helpful!
Laz
Hey everyone,
i am a newbie in IT, and i love IT network. I must a new design in a site, using 4 switches. There is a firewall also asa and a an ANIRA VPN mpls. I don’t know how i can create a design. I have an idea but i am not sure about it.
I was thinking to have 2 switches acting like core and distribution and each core has one interface to the firewall and one to the mpls router. And the swicthes will do load balancing for the lan access. My question it exists a firewall with 2 interfaces one to each core? same for mpls?
Maybe i must do another design. Thanks for your help.
stay safe all of you
Mina
Hello Mina
When you prepare to create a network design, you must first look at the requirements of the network. Questions that come to my mind reading your post include:
- How will this network connect to the Internet?
- Since MPLS is being used on the network edge, are we connecting to any remote sites?
- Do you want the firewall to be used only on the connection to the Internet or the connection to the MPLS network as well?
- How many hosts and what kind of traffic are you expecting to run on the network?
- What services will be running on the network?
- What level of redundancy do you want to achieve?
Now if you have a specific set of equipment that you can work with, then you are somewhat limited to what you can do. What you can achieve also depends upon the models of the devices you are provided with. Some things that you can achieve here include:
- Have two switches function as redundant core switches (I assume they are Layer 3) and run a First Hop Redundancy Protocol between them, such as HSRP. These will be performing all of the routing on your network.
- Connect both core switches to the firewall with two redundant links. Do the same with the connection to the MPLS router.
- Use the other two switches as access switches for your hosts with redundant links to the two cores.
All of this however is hypothetical. If you don’t have the information that I listed at the beginning, you cannot be more precise in creating a topology that will work. However, this will give you a starting point from which to begin. You can find out more information in the following lesson as well:
I hope this has been helpful!
Laz